In January, we launched real-time depeg detection across our stablecoin universe. In February, we expanded into structural vault risk scoring. In March, our systems were tested live during the USR collapse. In April, our systems continued to be tested and we learned and built off the lessons learned from the plethora of attacks this month, shoring up our defense and signal intelligence capabilities. April made one thing clear: DeFi defenders are losing the battle against attacker velocity. At the same time AI is accelerating legitimate engineering teams, it is also accelerating the capabilities of the underground economy. Campaigns that used to require a full specialist crew can now be executed by smaller groups using off-the-shelf AI tools. The outcomes are showing up in the data: incidents are more frequent, operations are more deliberate, and time-to-impact is shrinking.

28 incidents, roughly $635M lost. We were still dealing with the aftershocks of the USR attack and depeg in March, this incident already exposed how quickly stablecoin stress can spread through vaults and lending markets. Whether you look at Drift early in the month, Kelp DAO mid-month, or Wasabi at the end, the pattern was the same. These were not isolated failures. They were interconnected stress events in a tightly coupled system.
Something worth noting is that all of this is happening alongside a real market shift. Meme-coin momentum has cooled while capital is being funnelled into stablecoins and yield-bearing products. More institutional money moving through more complex infrastructure creates more systemic blast radius when something breaks. Naturally attackers are already adapting to that reality faster than most defenders.
When we look at a month like April we don't see 28 isolated incidents. We see the same pattern Webacy has been building toward for years: risk that was quantifiable before it resulted in losses. Someone had exposure to every one of those protocols. The question is whether they had any way to know what was coming. Here's what we shipped in April to shorten the window between an exploit happening and the losses that follow.
Contagion Is a Real Risk
When a protocol is exploited, the first-order loss is only the start. The real danger is second-order contagion: stress propagating through shared collateral, liquidity dependencies, and assumptions of stability. We saw this clearly in March with the USR minting exploit and the resulting stablecoin depegging. The damage did not stop with USR holders. It spread into vaults and lending markets that were treating USR as stable collateral, triggering deleveraging, liquidity stress, and liquidations. In April, Kelp DAO repeated the pattern at a larger scale. Roughly $292M was drained, rsETH depegged, and Aave faced up to $230M in exposure as rsETH-backed positions came under pressure. A bridge incident in one protocol quickly became a market-wide liquidity event.
This is the structural sequence we built into our monitoring:
- An exploit or governance shock hits a protocol
- A depeg, pause event, or liquidity dislocation follows
- Hidden dependencies across the broader ecosystem get exposed rapidly
To reduce response time, we shipped a real-time cascade monitor that detects depeg signals, liquidity shocks, and protocol pauses, then maps downstream exposure through a dependency graph: which vaults hold the affected asset, which lending markets use it as collateral, which stablecoins show correlated supply behavior.
In a scenario like Kelp DAO, that means as soon as rsETH begins to dislocate, we are already identifying exposed Aave markets and flagging collateral risk before broad repricing and liquidation cascades accelerate. That lead time is where defensive action becomes possible, and it is one of the most important system improvements we brought to production this month.

Redemption Queues: The Risk No One Was Watching
Redemption risk is straightforward in theory and brutal in practice. When many users try to exit simultaneously, either liquidity is sufficient and the system absorbs demand, or it isn't and confidence deterioration accelerates withdrawal pressure. That is classic bank run dynamics and the same principles apply in DeFi. Large single redemptions are a related signal, a significant single-wallet exit is often a leading indicator of broader stress. Sometimes the two risks compound: the dominant position in an unsettled queue belongs to a single wallet.
While building large-redemption monitoring, we found a category of risk that is broadly under-monitored: the unsettled redemption queue. In certain vault protocols, withdrawals don't happen automatically. A user submits a redemption request on-chain, it gets confirmed, the obligation is real and recorded. But it sits there until a curator manually processes it. No automatic settlement, no deadline, and no enforcement. The queue can grow indefinitely and from the outside the vault still looks completely normal. In one vault we found 19 pending redemption requests totaling millions of dollars, representing roughly 97% of the vault's TVL sitting in an unprocessed withdrawal queue. The oldest request was 45 days old. Every single transaction was confirmed on-chain. The users did everything right. They just haven't been able to get their money out. Before we built this monitoring, that vault was scoring as moderate risk. It now scores HIGH with a significant penalty for the queue state. That is exactly the type of blind spots we are trying to close.
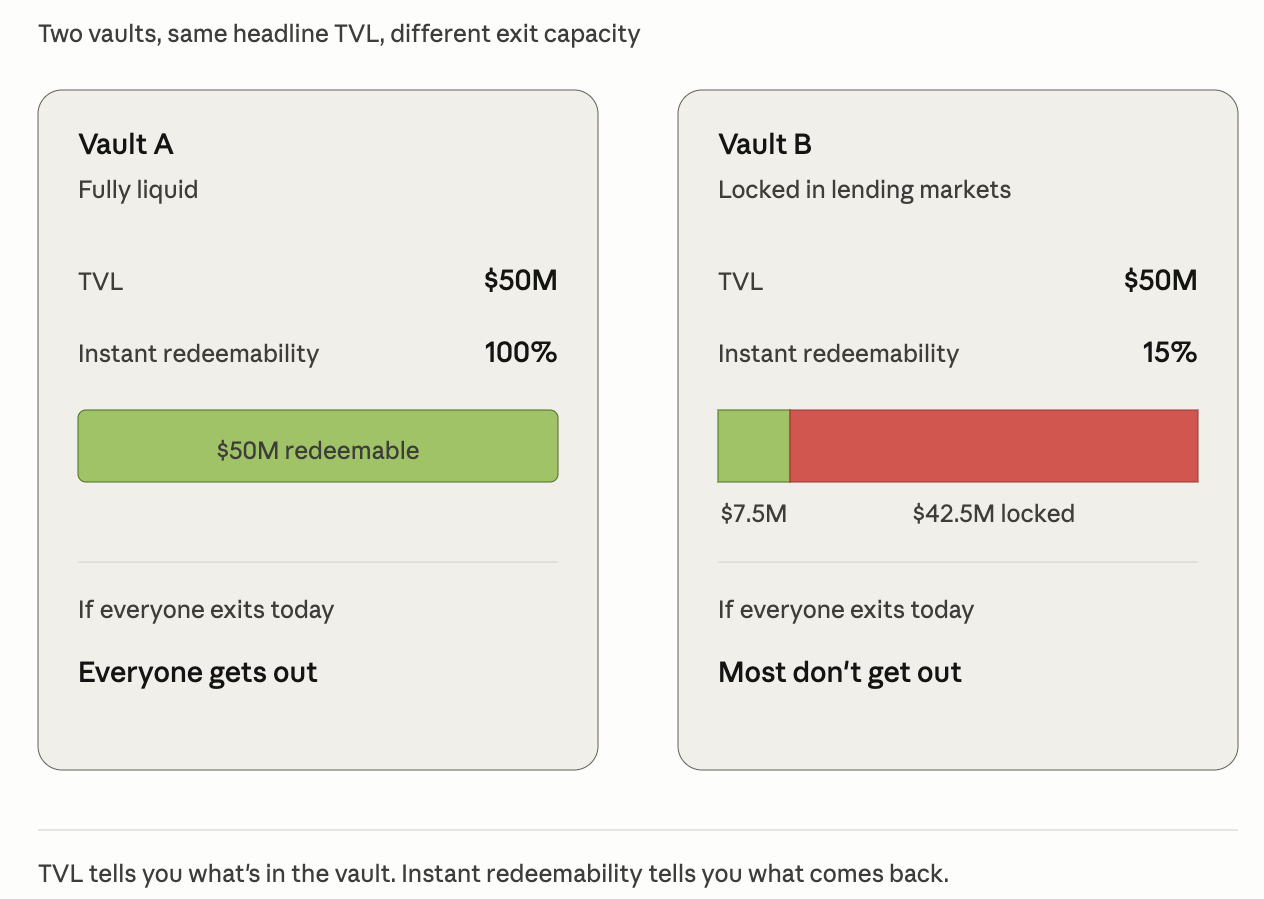
Instant Redeemability: What the TVL Number Hides
TVL is widely cited and frequently misunderstood. A vault showing $50M TVL does not imply $50M of immediate exit capacity. In a stressed market, when everyone is trying to leave at the same time, that gap is what separates the depositors who get their money back from the ones who don't. This month we shipped a per-market breakdown of what percentage of a vault's TVL can actually be redeemed right now, accounting for utilization, lockups, withdrawal queues, and liquidity depth across each underlying market. The metric runs at the market level, not just the vault level, giving a real picture of exit capacity rather than headline TVL. A vault with 15% instant redeemability and 85% locked in illiquid lending markets is a fundamentally different risk profile from one showing the same TVL with full liquidity. This signal gives us a ground-level measure of what a vault can actually return to depositors today, not what it says it holds.
Audit Quality, not Audit Count
Something worth noting about April's hacks: many of the exploited protocols had audits. Drift had multiple audits from reputable firms. The code wasn't the problem in these incidents. The attack came through social engineering, compromised keys, and bridge infrastructure that audits don't typically cover.
That shift in the attack surface makes audit quality even more important as a signal. When a protocol does get hit through its code, the question of who reviewed that code matters enormously. A Trail of Bits or OpenZeppelin engagement means experienced researchers with years of protocol-specific expertise look for vulnerabilities. An audit from a shop nobody has heard of might mean a two week review that gave the protocol a clean report and a logo to put on their website. An audit from an unrecognized firm may not just fail to catch bugs, but can also create a false sense of legitimacy that users and integrators rely on.
In February we introduced audit history as a scoring input. In April we deepened it with tiered firm classification and named-firm weighting. A vault with one review from a top-tier specialist should not score the same as a vault with multiple low-signal audits of uncertain depth. We’re not just taking into account raw audit count as a signal. We are incorporating the confidence that the right expertise examined the right surfaces with sufficient rigor.
Governance Risk Signal Improvements at Scale
Kelp DAO's core governance was not the attack surface the exploit came through bridge infrastructure. Wasabi had a single deployer key holding ADMIN_ROLE across its deployments, with no multisig and no timelock between granting a role and using it, USR was a minting key compromise. Three of the most recent biggest incidents came down to the same underlying question: who actually controls this protocol, and is anyone monitoring for changes in those controls. For the most part we cannot stop a private key from being compromised, that's an operational security tale as old as time and the problem will continue. What we can do is shrink the window between compromise and impact. We shipped two governance surveillance capabilities in April to address this directly:
The first is MINTER_ROLE monitoring for stablecoins. We now track on-chain mint authority grants and revocations across every monitored stablecoin. When a new address is granted the ability to mint, or an existing minter's role gets revoked, it surfaces in the daily digest immediately. The USR collapse had a detectable on-chain signature before the damage was done. Tracking who holds minting authority and when it changes is a foundational signal for early-warning systems.
The second is upgrade caller classification for vault governance events. We now identify whether governance actions are being executed by an EOA or a contract, and surface multisig configuration and timelock duration as structured fields in vault scoring. A protocol can have a timelock on paper and route around it in practice. An admin action executing from a bare EOA when a multisig is expected is a signal. An upgrade call in the same block as a proposal is a signal. We’re extracting signals to score governance quality now and not just its presence.
Conclusion
For a majority of incidents the signals were there before the losses happened. It was on-chain. In redemption queues no one was watching. In bridge configurations flagged awhile ago. In admin keys with no risk monitoring on them. The structural conditions were detectable before the price ever moved, the same pattern we saw with USR in March and Kelp DAO in April, are the same types of patterns that will define future incidents.
The common theme across everything we shipped this month is encapsulated by a single question: when a user needs to exit, are they able to withdraw/redeem their funds? The idea sounds simple and logical, but oftentimes not as straightforward as it seems. A vault can look healthy on every surface metric while quietly trapping capital. TVL tells you what's in the vault, but it doesn't tell you what's redeemable. The instant redeemability signal, the redemption queue monitoring, and the large-redemption alerts are all trying to answer the same questions from different angles: if you tried to redeem your funds today, would you actually get the money back? We found a vault this month with 97% of its TVL sitting in an unprocessed withdrawal queue for over 6 weeks. Every transaction was confirmed on-chain. The users did everything right. That's the kind of thing that doesn't show up anywhere until you build something specifically to look for it.
The governance and contagion work connects to the same question at a different layer. Protocol failures and cascades are ultimately forced, disorderly exits, unevenly distributed, with the worst outcomes for whoever finds out last.
And increasingly, the adversaries on the other side of these incidents are using AI to find those gaps faster and exploit them with more precision than ever before. The only reasonable response is to learn from community failures and apply those lessons and build systems that close the gaps sooner.










