The numbers in this report represent a sample of the poisoning events detected across wallets actively queried through Webacy's API by our customers and partners protecting real users in real time. This is not a passive full-chain scan, every event here represents a wallet that someone is actively protecting.
TL;DR
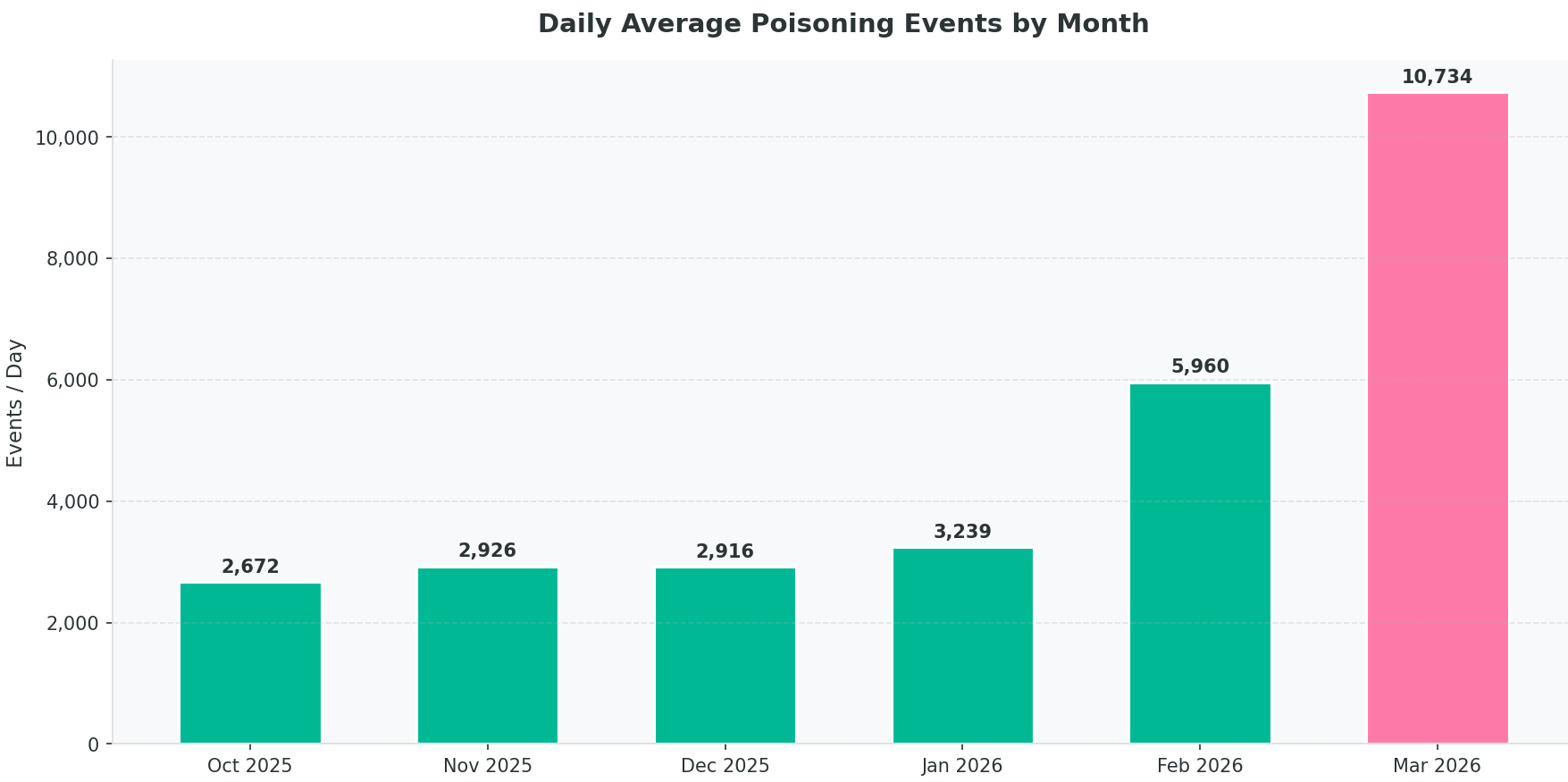
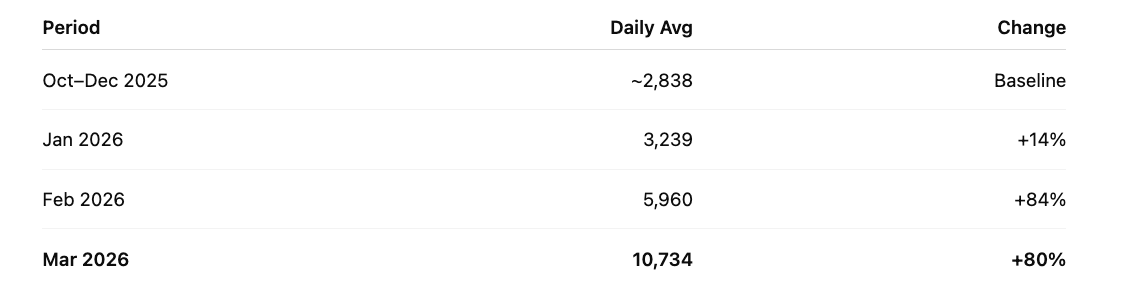
Address poisoning activity is accelerating rapidly. After a steady baseline of roughly 2,800 events per day in Q4 2025, activity surged in early 2026, reaching 10,734 events per day in March, a 4× increase from October levels. In just 12 days, March has already produced 128,803 poisoning events, nearly matching entire months in late 2025. At the current pace, March is projected to exceed 330,000 events, more than double any previous month. Attacks are also expanding beyond Ethereum. Layer-2 networks such as Base, Arbitrum, and BSC now represent a growing share of poisoning activity. Despite this surge, our XGBoost detection model maintains ~99% accuracy across all supported chains.
Address poisoning isn't a niche attack vector anymore. It's a scaled, multi-chain campaign running around the clock against real users.
The numbers from the last six months tell a clear story: this threat has entered a new phase.
What address poisoning actually is
Address poisoning occurs when an attacker sends a zero-value transaction from an address that closely resembles one the victim has previously interacted with. The goal is to trick the victim into copying the attacker’s address from their transaction history or recent-address list, causing funds to be sent to the attacker. These attacks exploit a common wallet UI pattern: addresses are truncated, displaying only the first and last few characters. Attackers generate vanity addresses with matching prefixes and suffixes, making them difficult to distinguish at a glance. All poisoning transactions in our dataset carry zero value, their sole purpose is to pollute transaction history.
No smart contract exploit. No phishing link. Just a copy-paste mistake, engineered at scale.
The numbers: Q4 2025 through March 2026
We analyzed a sample of six months of address-poisoning data from the production detection pipeline:
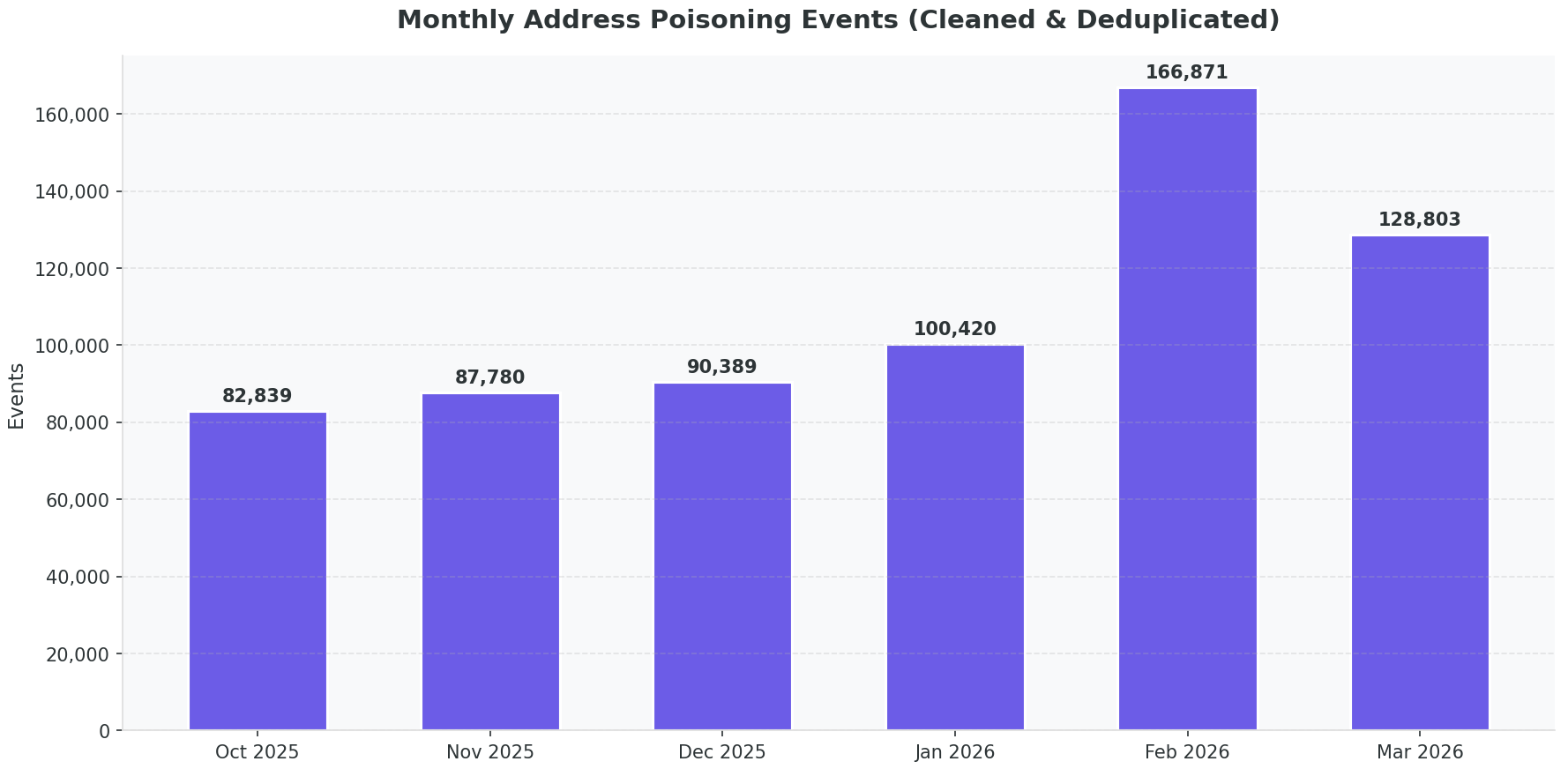
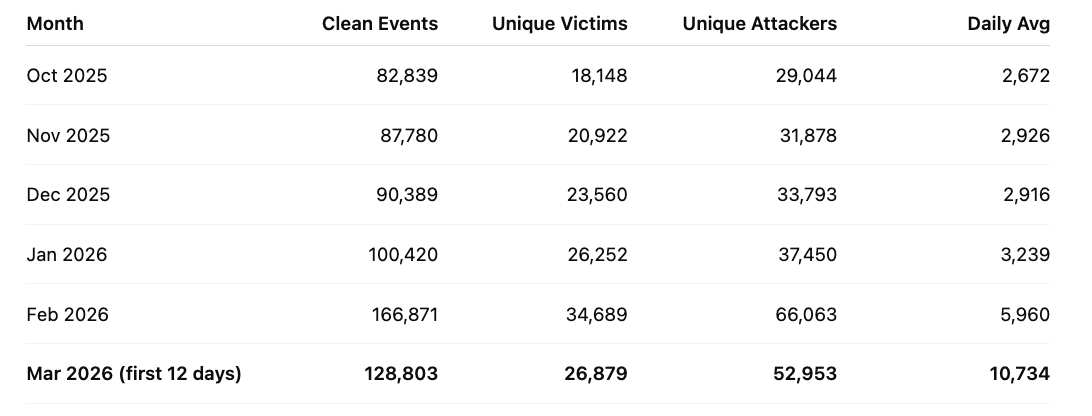
At only 12 days into March, it is already at 128,803 events. At the current pace, the month is projected to reach ~330,000 poisoning events, which would be more than double any previous month in the dataset.
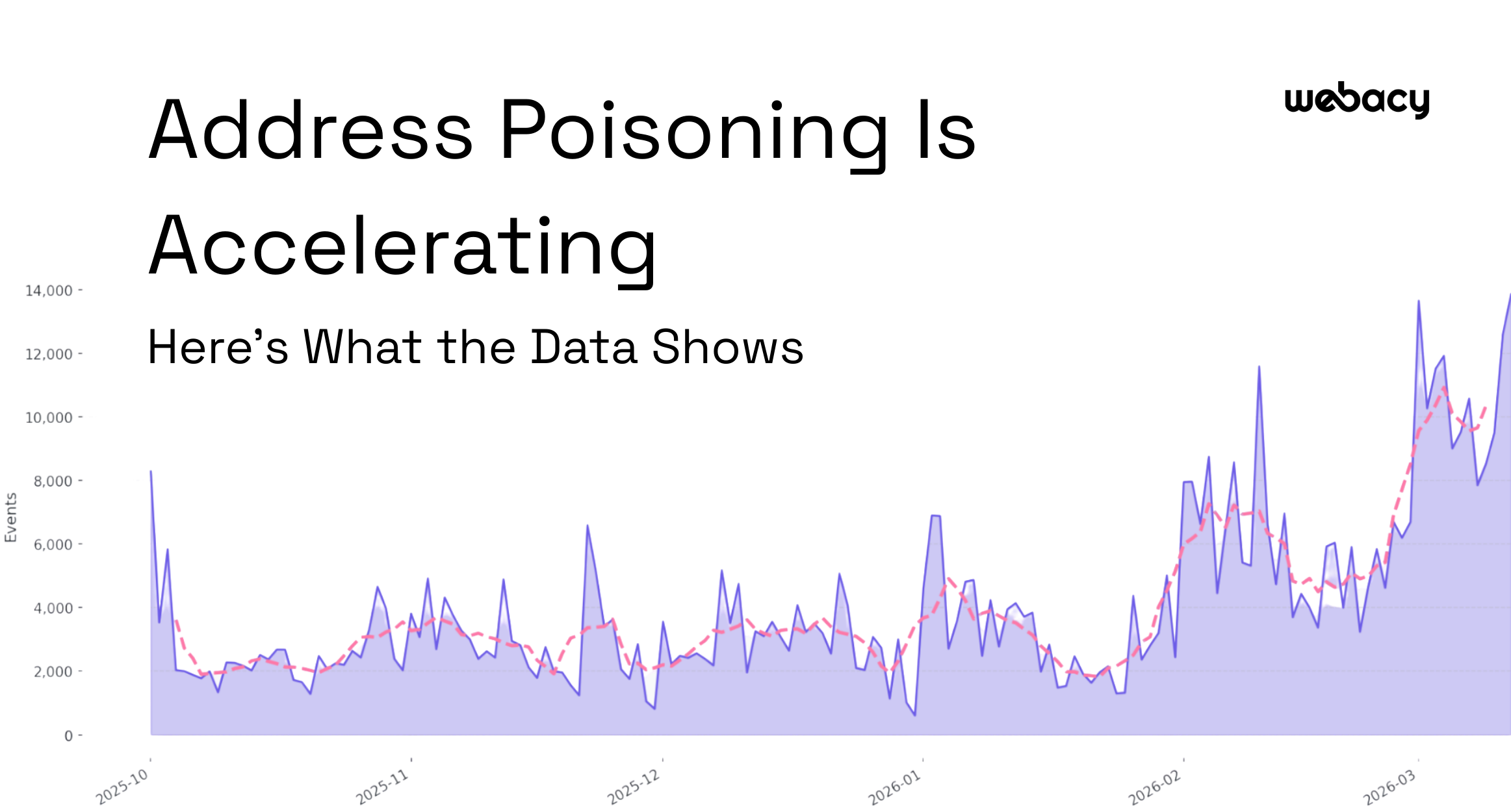
Daily Trend
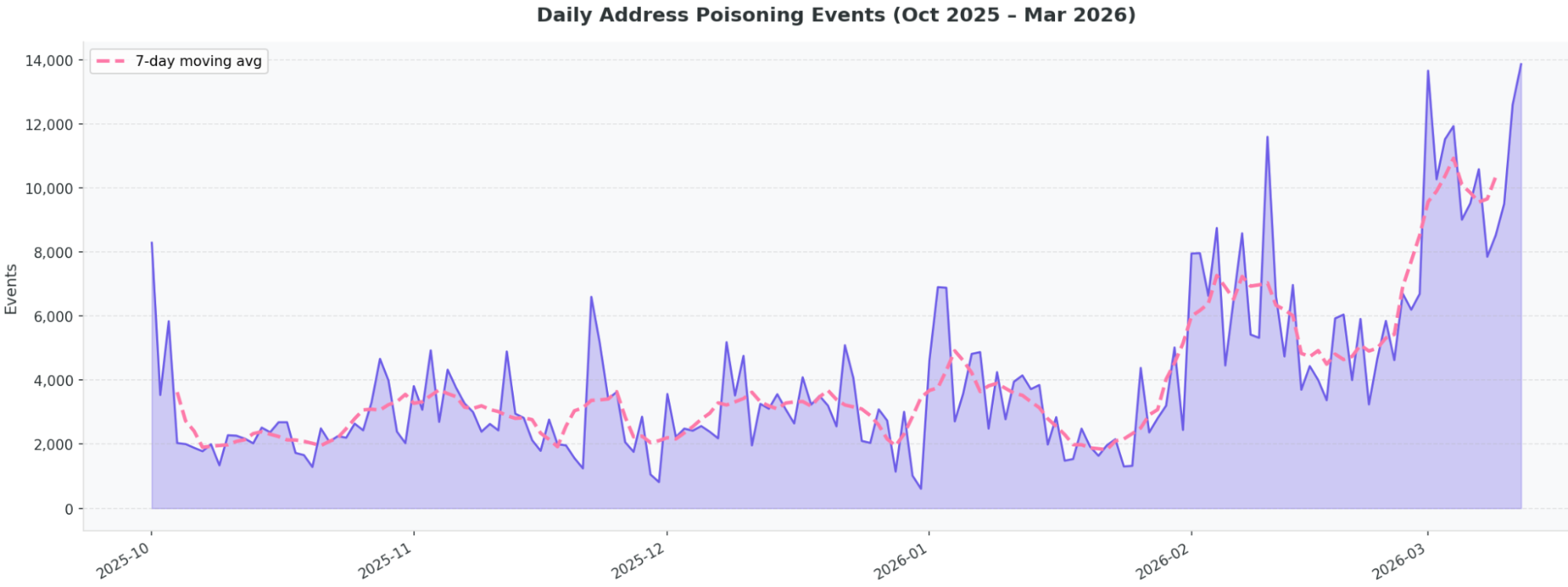
The 7-day moving average shows a clear pattern:
- Q4 2025: stable baseline between 2,500–4,000 events/day
- February 2026: sharp inflection point
- March 2026: sustained activity above 10,000/day
We see a clear acceleration in daily activity.
Multi-Chain Expansion
Ethereum remains the dominant target, but attacks are spreading across multiple chains.
Base has become a consistent second or third most-targeted chain in our data. Arbitrum is an emerging attack surface. BSC saw a major spike in February. Optimism spiked in October before stabilizing.
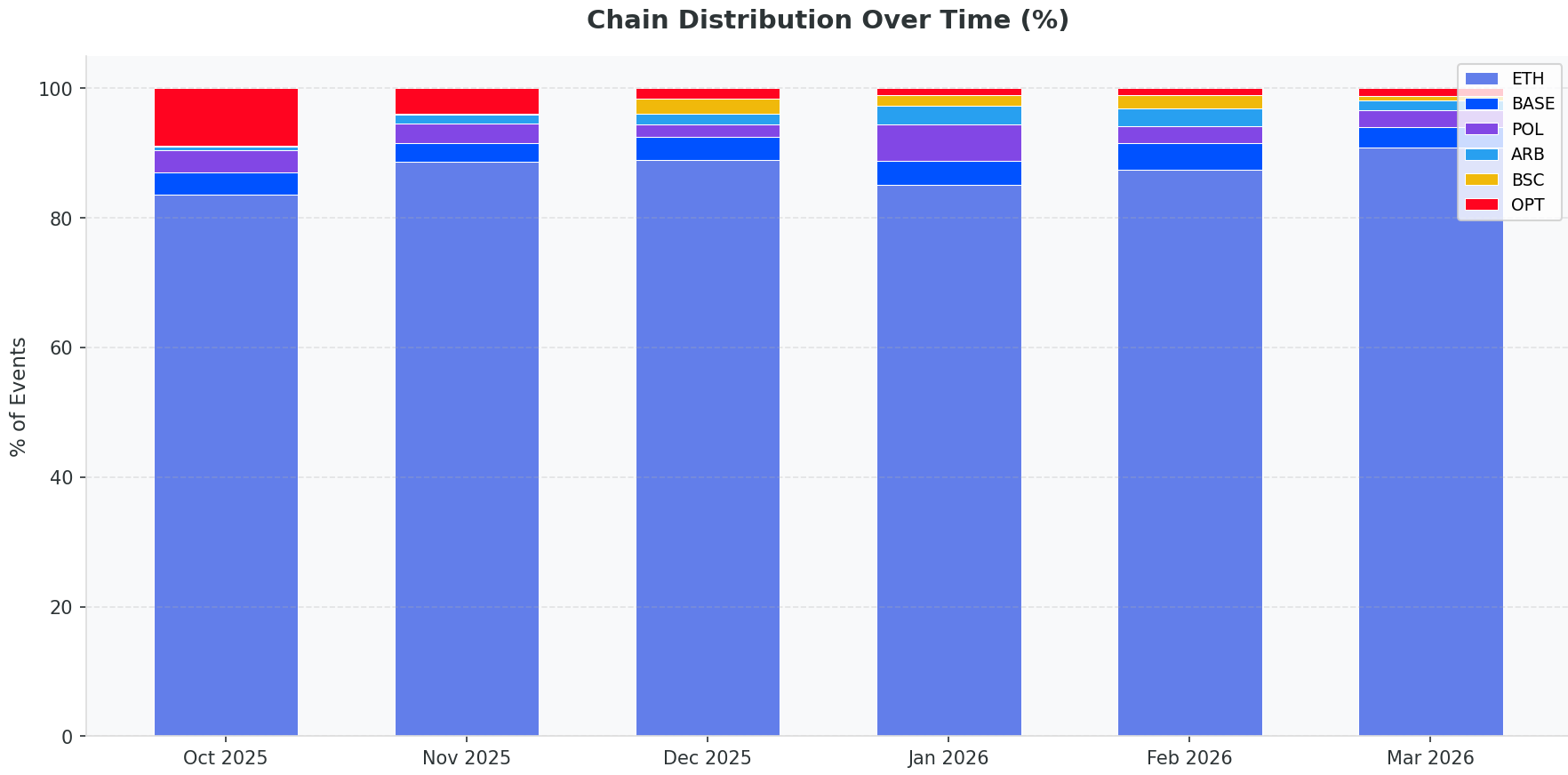
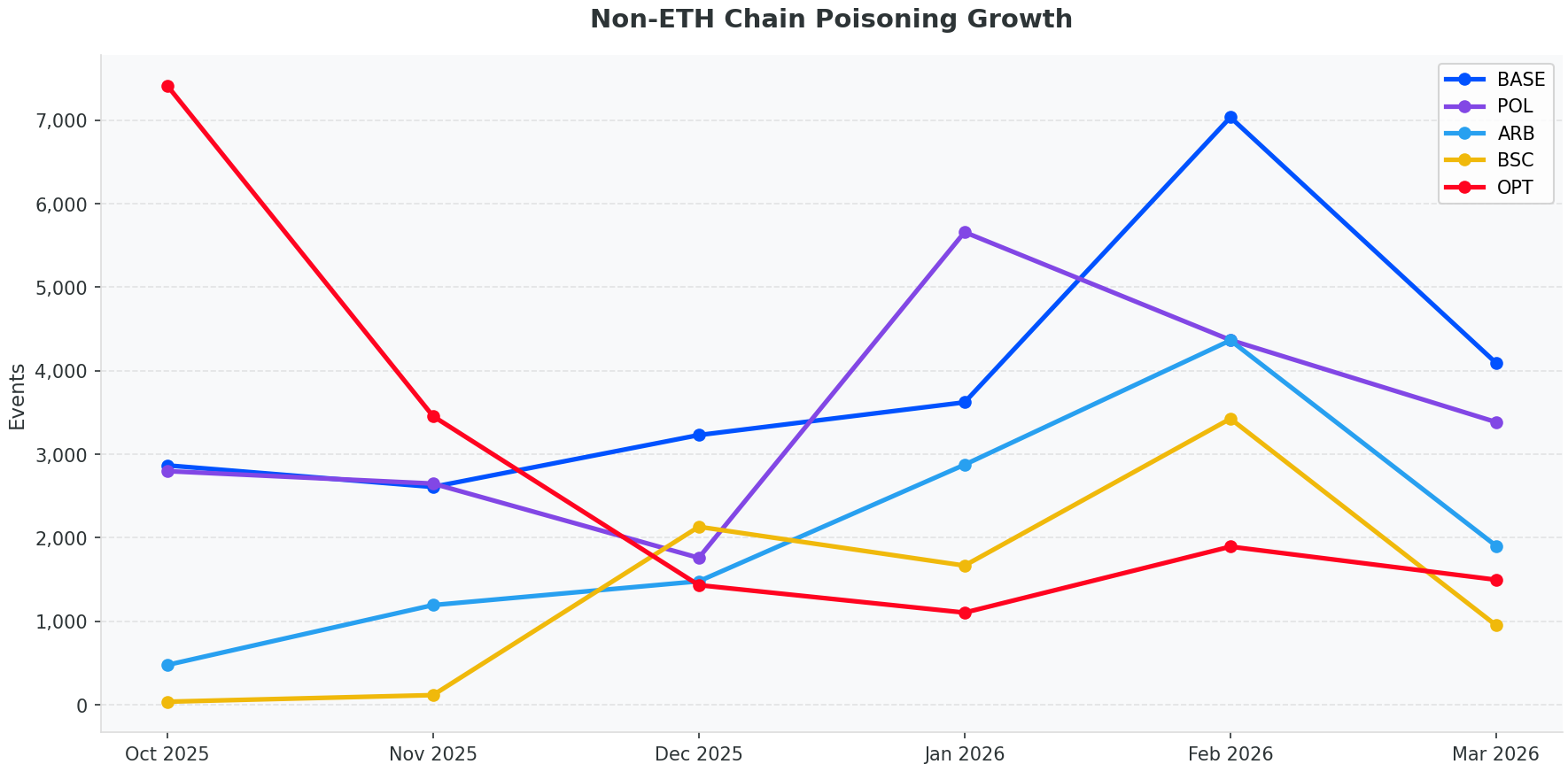
The implication is straightforward: if your wallet or dApp operates on any L2, you need the same poisoning protections you'd expect on mainnet. Attackers go where the users are.
Attackers are scaling, not just increasing
One of the more telling signals in our data is the attacker-to-victim ratio. In October 2025, there were roughly 1.6 unique attacker addresses per victim. By February 2026, that ratio had climbed to 1.9.
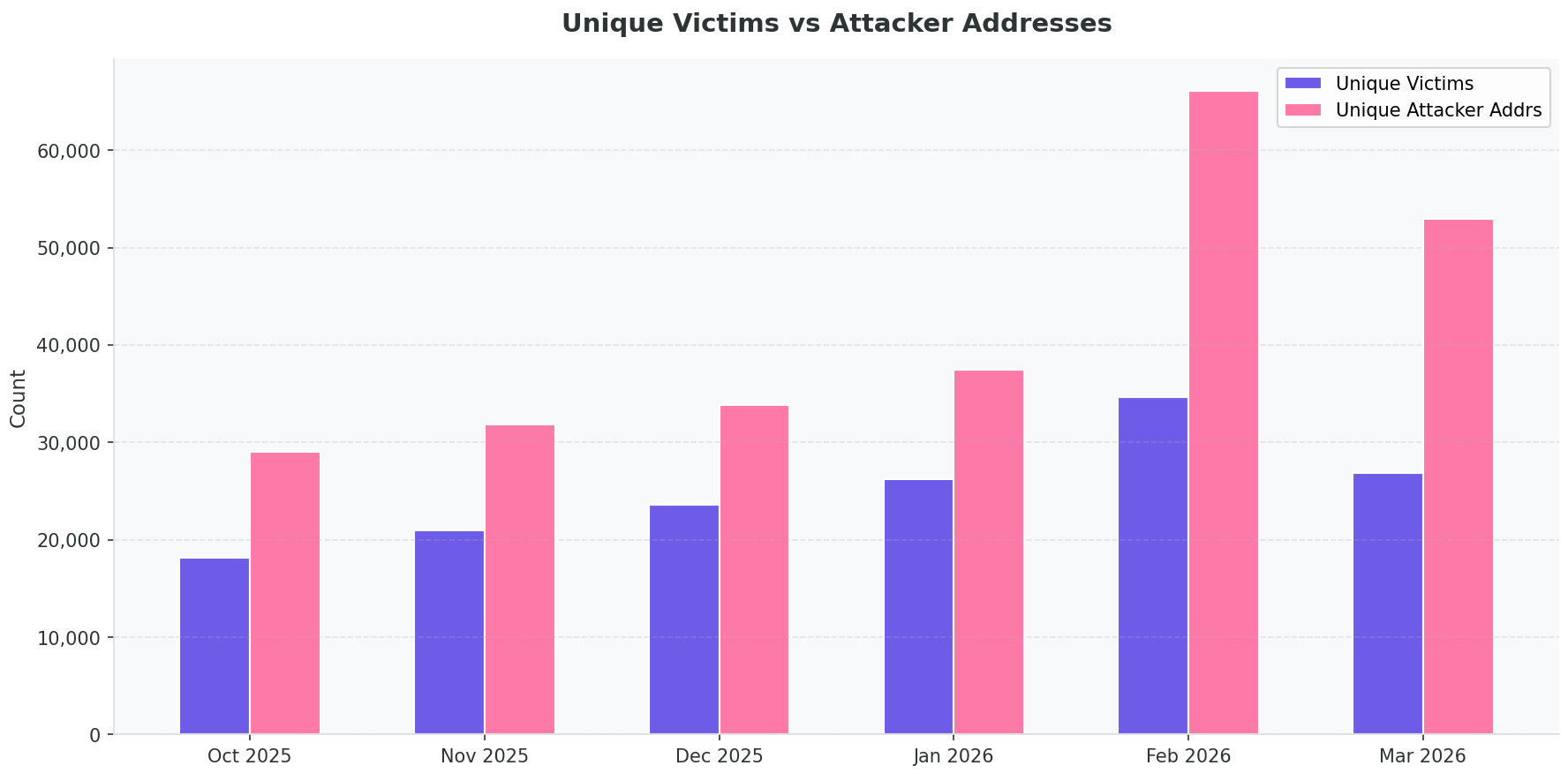
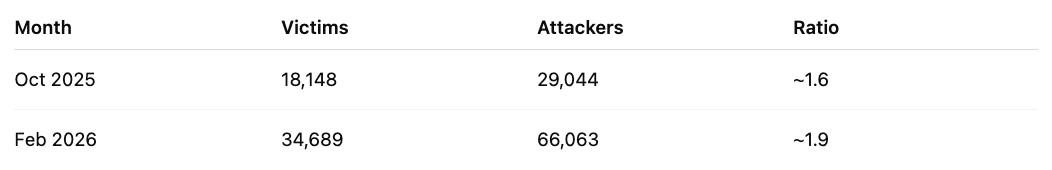
Attackers aren't just running more campaigns. They're rotating through larger pools of spoofed addresses per campaign, making static blocklists less effective and increasing the odds that a poisoned address appears in a victim's recent transaction history.
How we detect poisoning
Our detection system combines heuristic analysis with an XGBoost classifier trained on 94 features, including sequence similarity, Levenshtein distance between addresses, prefix-suffix edit distance, transaction value, sender transaction count, token name anomaly detection, and familiar-address matching against wallet history.
Each transaction receives a probability score between 0 and 1. Three-stage filtering keeps false positives low without compromising coverage.
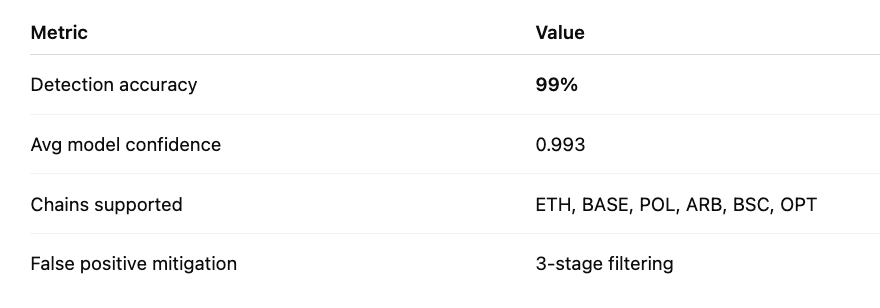
As of March 2026, the model maintains 99% detection accuracy with an average confidence score of 0.993 across ETH, Base, Polygon, Arbitrum, BSC, and Optimism.
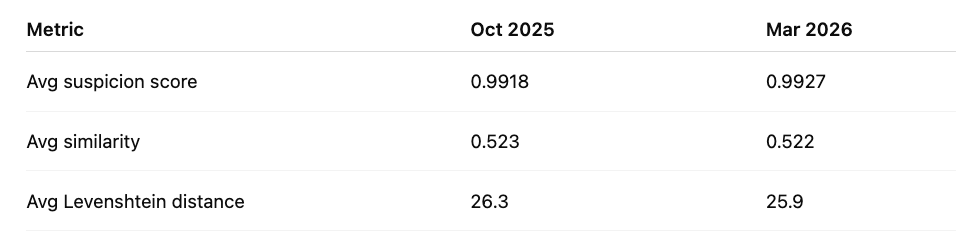
One note worth flagging: attackers are producing slightly closer address matches over time. Average Levenshtein distance dropped from 26.3 in October 2025 to 25.9 in March 2026. They're getting more precise. The model is keeping pace, but the arms race is real.
What to do now
If you operate a wallet, exchange, or dApp:
- Hide zero-value transactions from address suggestions and recent-address lists
- Warn users when a near-collision address appears that closely resembles one they've used before
- Collapse or label known poisoning patterns in transaction history UI
- Maintain a trusted address book for frequent destinations
- Integrate real-time transaction risk scoring so suspicious addresses are flagged before funds move
Address poisoning works because wallets make it easy to copy addresses from history. The fix starts at the interface level, backed by real-time intelligence.
Talk to us
Webacy's address poisoning detection is live with 99% accuracy and 3-stage false positive filtering. If you want to understand how to integrate protection for your users, get in touch.